Hook
Digital does not automatically mean defensible.
That is the part many teams miss. A system can be electronic, timestamped, and password protected and still leave the audit story broken when someone tries to review it later.
Real-world scenario
A QA team opens a deviation in one tool, pushes the investigation into another, and records the Corrective and Preventive Action (CAPA) in a third.
Each system has its own timestamps. Each record looks fine on its own. But when an auditor asks how the event moved from issue to investigation to closure, the story has to be reconstructed across tools.
That is where audit trails fail in digital environments: not because the system is missing data, but because the data is no longer attached to one clear record.
Audit pain moment
An auditor does not usually begin with a long technical discussion.
They ask a simple question: show me how this deviation moved from identification to closure.
If the answer requires opening four systems and explaining gaps manually, the audit trail has already failed its most important test.
What an audit trail is supposed to do
FDA guidance treats audit trails as part of the evidence that protects record authenticity and integrity. In practice, an audit trail should help a reviewer answer:
- who changed the record
- what changed
- when it changed
- whether earlier entries are preserved
- whether the history can be reviewed without guesswork
When those conditions are met, the audit trail helps the team rebuild the story. When they are not, the trail becomes decoration.
Why digital systems still fail
The failure usually comes from system design, not from the idea of a digital record itself.
| Common problem | What happens in practice |
|---|---|
| Fragmented workflows | The event, investigation, and closure live in different places |
| Weak permissions | Users can edit content without a strong owner model |
| Overlapping tools | One system holds the history, another holds the decision |
| Poor review discipline | Audit trails exist, but nobody uses them to review the record |
| Copy-paste control | The history is manually recreated in summaries instead of preserved in the source record |
What fragmented audit trails cost
Fragmented trails do not only create inspection risk. They also create hidden operating cost.
- QA time gets spent rebuilding evidence instead of reviewing quality.
- Audits take longer because the team has to reconcile multiple systems.
- Batch or release decisions can stall while history is reconstructed.
- Repeated observations become more likely when the same record weakness appears again.
Leadership usually feels this as delay, duplication, and avoidable escalation. QA feels it as frustration and rework.
Where audit trails break in practice
| Audit trail expectation | How it fails | Why it matters |
|---|---|---|
| Chronological history | Events are not linked in sequence | Reviewers cannot follow the story |
| Attributable changes | Shared logins or unclear ownership | You cannot defend who did what |
| Complete record history | Earlier context is overwritten or lost | The record no longer explains itself |
| Reviewable changes | Audit data is hard to find or hard to read | The trail exists but is not useful |
| Available evidence | Teams need to rebuild the trail from exports | Inspection response becomes slow and fragile |
A short comparison
| Manual or fragmented digital setup | Governed digital workflow |
|---|---|
| Audit data is spread across tools | One workflow preserves the sequence |
| QA must rebuild the story later | The story stays attached to the record |
| Approvals are visible only after export | Approvals are part of the action |
| Review takes time and interpretation | Review is faster and more defensible |
That is the real difference between having audit trail data and having an audit trail that helps you.
What regulators are looking for
FDA guidance on Part 11 and related data-integrity materials keeps pointing teams back to the same principles: records must be trustworthy, and changes should not obscure what came before.
That means digital systems need more than timestamps. They need:
- controlled changes
- reviewable history
- preserved context
- retrievable evidence
- a workflow that keeps the record coherent over time
If the system makes the team work backwards from exports and screenshots, the trail is too weak.
What a better system changes
A governed eQMS changes the role of the audit trail.
Instead of being something QA inspects after the fact, it becomes part of how the process is controlled:
- changes are captured in context
- approvals stay attached to the record
- follow-up actions stay linked to the original event
- review is part of the workflow, not a separate cleanup exercise
That makes inspection response much more practical. Audit trails do not fail because they are missing. They fail because the system does not preserve the relationship between events, decisions, and changes. In a better system, the audit trail is not a separate artifact that QA has to go hunting for later. It is governed evidence that stays attached to the workflow history from the start.
Download template
If your team is evaluating audit trail readiness, a short checklist can help expose where the record is still fragmented.
The checklist should ask:
- Can we reconstruct the full sequence?
- Are changes attributable?
- Are approvals attached to the same record?
- Can QA review the trail without exporting everything manually?
That is the quickest way to see whether the system is actually holding the story together.
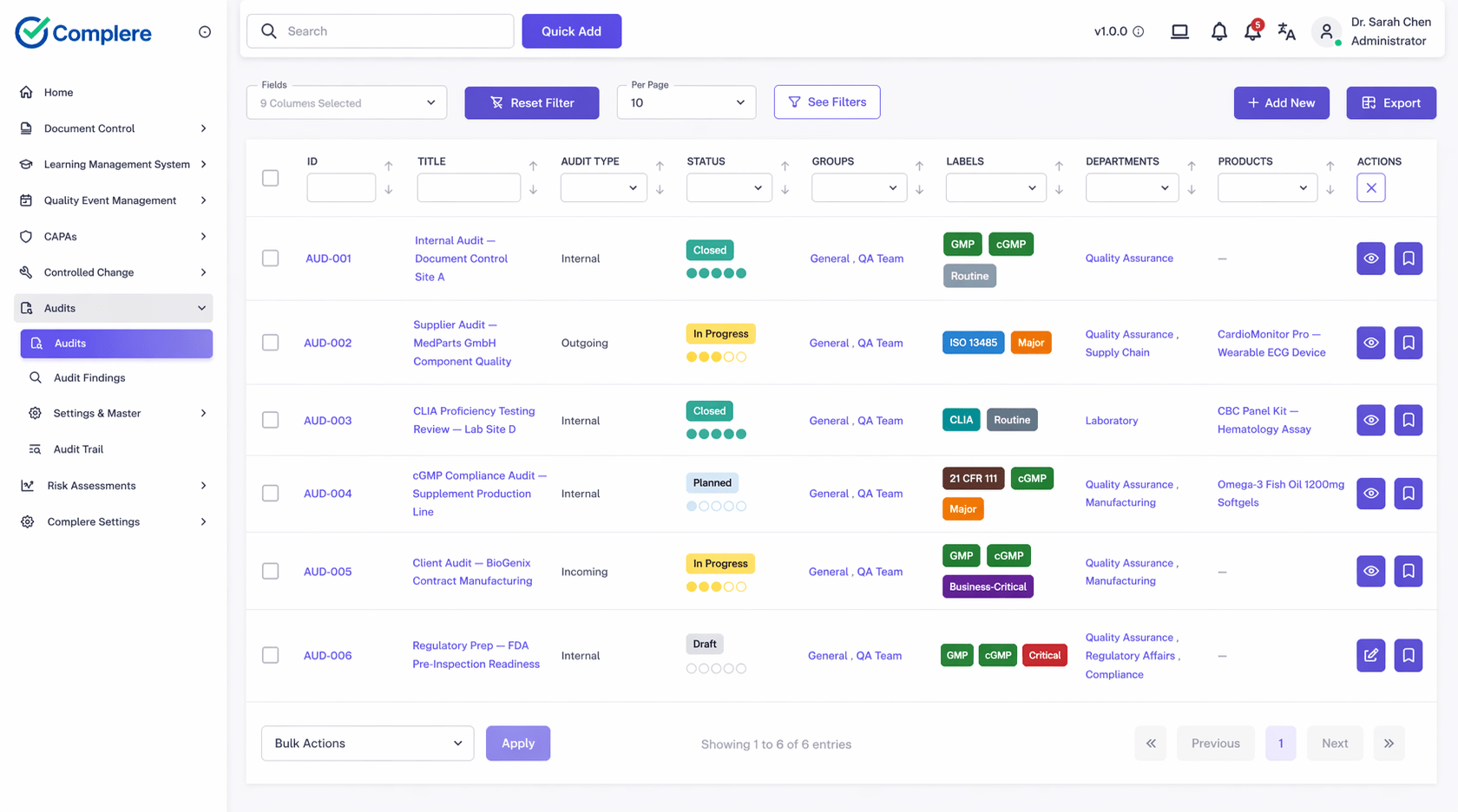
Complere fit
Complere matters here because audit trail control is not only about storing history. It is about keeping the event, the change, the approval, and the follow-up attached to the same governed record so QA does not have to reconstruct the story from exports and screenshots.
Complere does not generate more audit trail data. It keeps governed evidence attached to the workflow history the record is supposed to explain.
That kind of control becomes valuable the moment an inspector asks a direct question and the team needs one source of truth instead of four disconnected systems. In practice, Complere helps regulated teams preserve traceability, reduce evidence stitching, and defend record history with less manual effort.
Closing thought
An audit trail is not useful because it exists.
It is useful because it helps the team explain what happened without turning the review into a reconstruction exercise.
That is why audit trails are not just a feature. They are a system property. The strongest systems make that property visible without manual reconstruction.
Disclaimer
This article is a practical interpretation of FDA data-integrity and Part 11 expectations and is not legal advice. Teams should assess audit-trail controls against their own process, intended use, and validation approach.